Microsoft’s Security Testing and Offensive Research Team (STORM) disclosed that there are multiple vulnerabilities in the Windows Recovery Environment (WinRE) that can be exploited to bypass BitLocker encryption and steal fully encrypted data.
IT Home Note: WinRE is a key recovery function of Windows 10 and Windows 11 systems, mainly used after system crash or damage, users can hold down the Shift key through the login interface to restart and enter, and repair system failures through an independent operating environment.
BitLocker (known as “Device Encryption DE” on some devices) is a core protection against physical attacks in Windows, protecting data at rest with full-volume encryption.
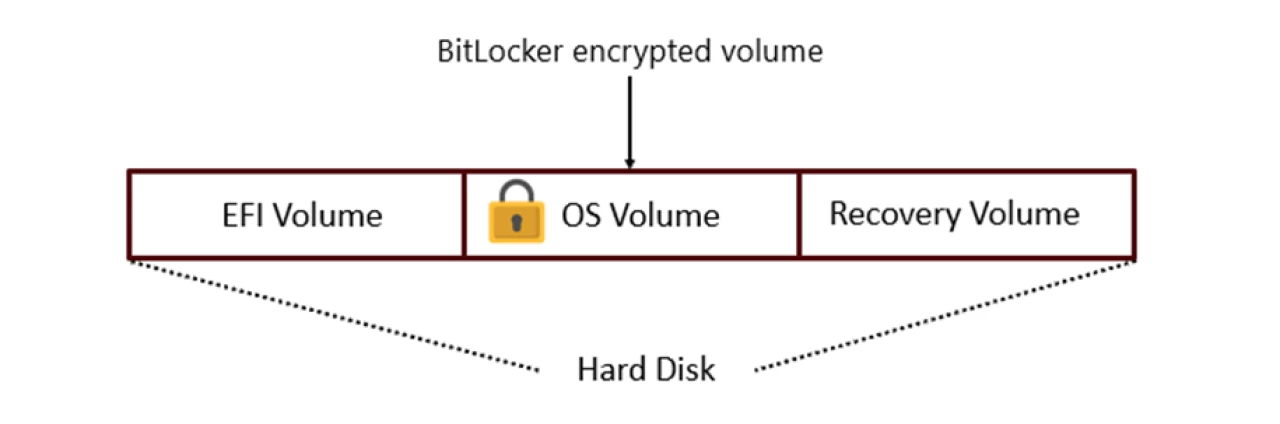
To ensure that the system can be restored after BitLocker is enabled, Microsoft has adapted the WinRE architecture to move its image (WinRE.wim) to an unencrypted recovery partition and introduced a “trusted WIM boot” mechanism to verify image integrity, while triggering a volume relock when running a high-risk tool such as a command prompt, which requires a recovery key to continue.
The study found that WinRE can access files in the EFI system partition and recovery partition once it enters the “auto-unlock” state with trusted verification. Attackers can exploit many of these vulnerabilities to manipulate WinRE to execute malicious code, extract BitLocker keys, or directly copy encrypted data.
The relevant vulnerabilities, numbered CVE-2025-48800, CVE-2025-48003, CVE-2025-48804, and CVE-2025-48818, have been fixed in the cumulative update released on the Tuesday Patch Event Day in July 2025, Microsoft urges Windows 10, Windows 11 systems to install the update as soon as possible, and since the update is cumulative, users can choose to install the latest August cumulative update.