Security researchers have discovered a new type of FIDO downgrade attack that can bypass the FIDO authentication mechanism in Microsoft Entra ID, enticing users to log in using weaker authentication methods, thereby exposing them to man-in-the-middle phishing attacks.
FIDO is the abbreviation for Fast Identity Online, a set of open standards aimed at achieving passwordless authentication and enhancing account security.
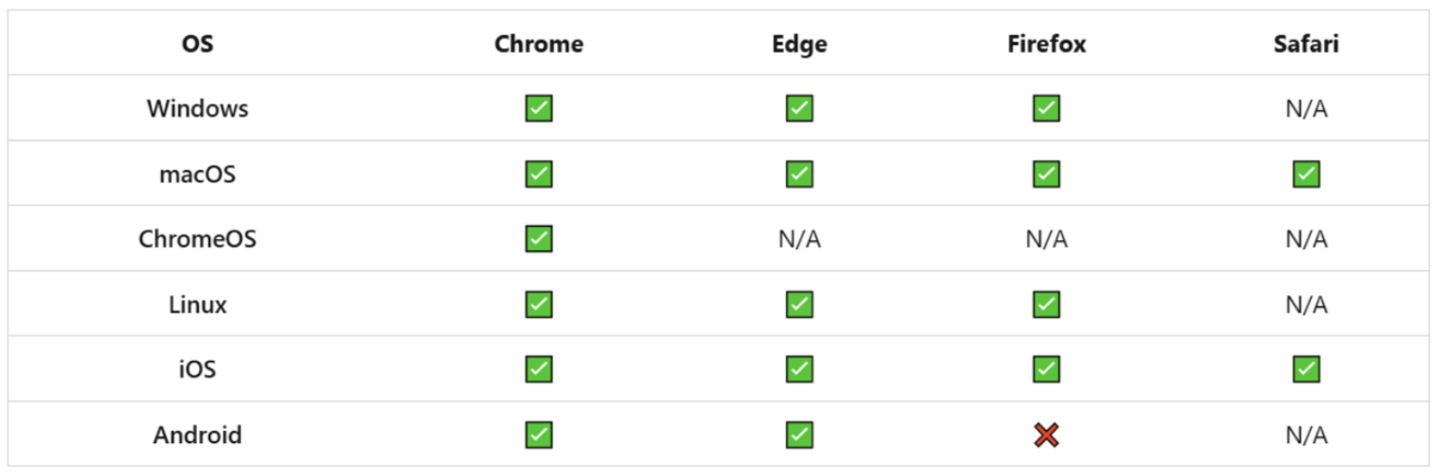
Security experts from Proofpoint recently disclosed a new FIDO downgrade attack, which does not exploit vulnerabilities in the FIDO protocol itself, but instead, by manipulate the browser User Agent (a string that the browser identifies itself to the server, used to determine device and browser compatibility) information, masquerade as an environment that does not support FIDO, causing the system to automatically disable FIDO authentication and prompt users to choose other verification methods.
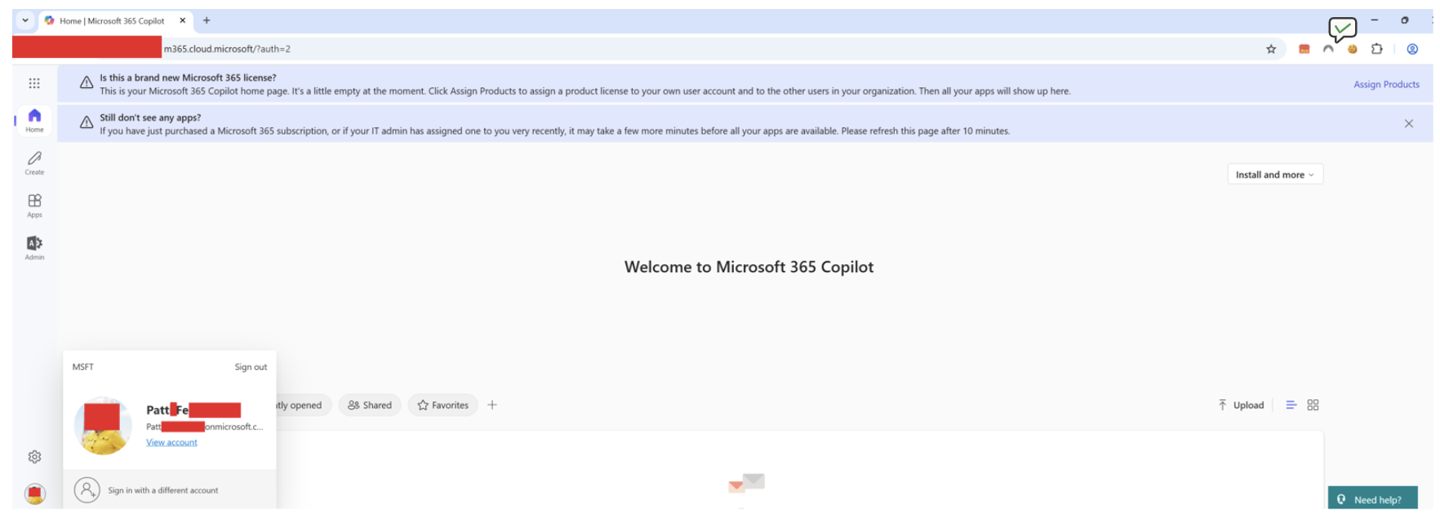
The attack begins with a phishing link, which, when clicked, redirects the user to a faux login page (set up by an intermediary attack framework such as Evilginx), which proxies the real Entra ID login form, but the “phishlet” module configured by the attacker forging a User Agent that does not support FIDO.
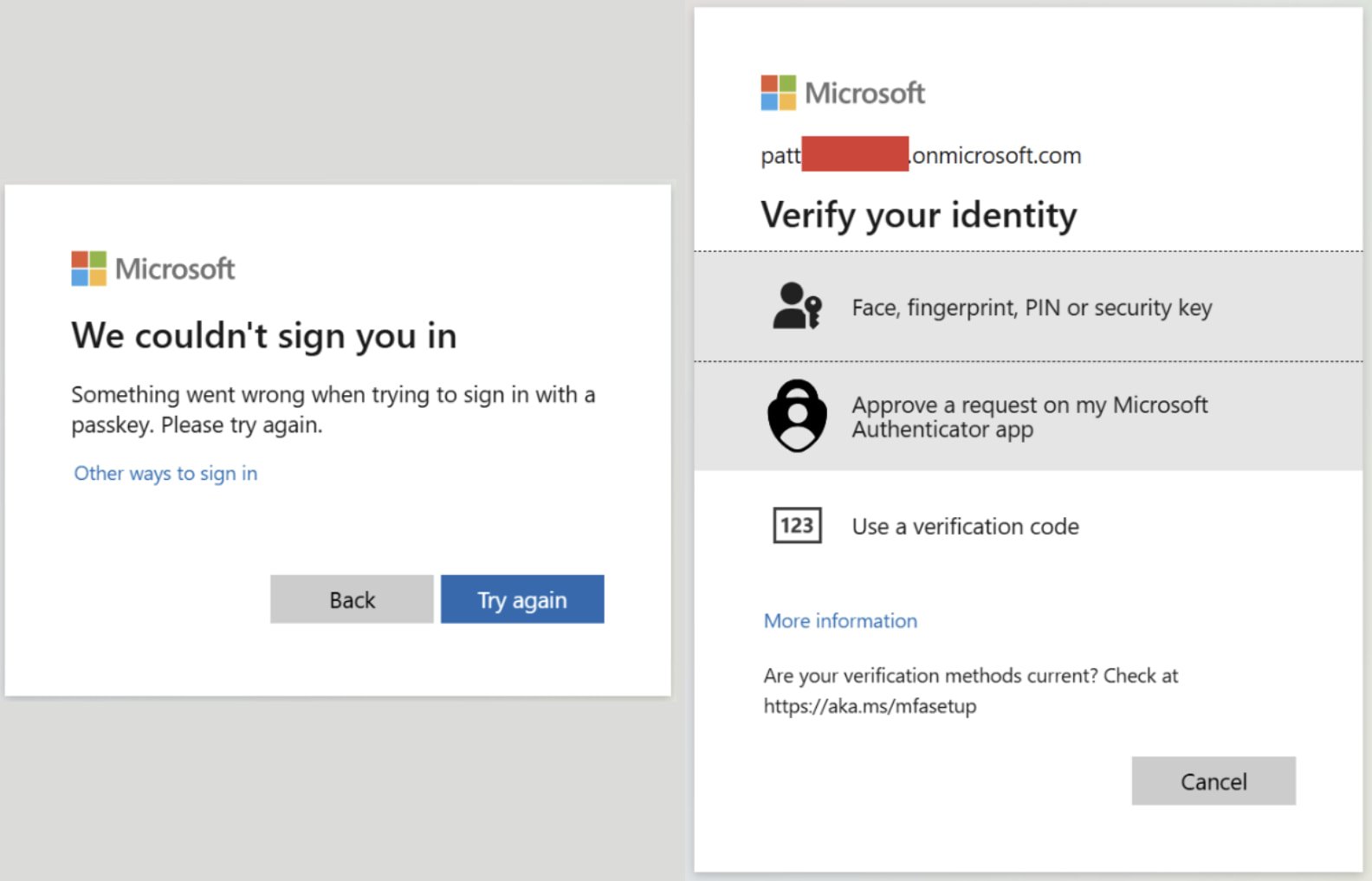
After the system detection, the FIDO function is disabled and an error message is returned, guiding the user to choose alternative methods such as Microsoft Authenticator app, SMS verification code, or one-time password, whose verification data can be intercepted during transmission.
Once the user completes the alternative verification, the attacker can obtain the full login credentials and session Cookie through a proxy server and import them into a local browser, taking full control of the account. While no wild exploitation cases are known at the moment, the attack is applicable to highly targeted advanced persistent threat scenarios.